What is Environmental Monitoring?
Data center equipment relies on high environmental standards for stellar performance and energy-efficient operations. While your business’s technology includes many nonphysical components, the physical settings of your computer rooms and other IT areas need to be at ideal operating conditions for equipment to function properly.
Environmental monitoring is the process of making sure a tech environment is suitable for its intended purpose. Many industries use environmental monitoring to ensure employees and data center equipment can perform their functions safely and efficiently.
Technology’s physical components need ideal conditions, which can change based on external factors in your building or the overall climate, as well as heat generated by the machines’ internal operations. Some environmental monitoring systems let you track conditions as changes arise, while others alert you to potential dangers or data management interruptions. Being able to monitor minute changes in an office or data center makes it less likely that a small action or environmental imbalance turns into devastating damage to equipment and networks.
Environmental Factors to Monitor
The purpose of environmental monitoring is to keep critical spaces in the correct state for optimal performance and security. A complete environmental monitoring system allows you to keep tabs on the following factors:

1. Temperature
Temperature is a critical factor to monitor in a data center. Data center cooling requires smart planning to be efficient, and many things can go wrong if the temperature is not monitored adequately. If a data center can’t dissipate its heat quickly enough, the risk of damaged hardware and lost data goes up. If the data center is kept too cool, it will cost the business in wasted energy.
Even a slight tweak in temperature can make a significant difference in operating costs. Estimates suggest allowing a one-degree increase in temperature can save about 2 to 3% of energy consumption. No matter the size of your data center, that percentage can make a big impact on the budget. However, it’s essential to make sure the temperature doesn’t increase beyond set thresholds.
Temperature monitoring involves sensors placed in multiple areas. The top, middle and bottom of racks should all be monitored, as well as the intake and discharge vents of the AC system. Critical devices should also have sensors. Within a rack-mounted device, the temperature could easily be 10 or 20 degrees higher than the ambient temperature in the room. Temperature monitoring allows you to gauge the efficiency of your cooling system and make adjustments when necessary.
2. Humidity
Like temperature, too much or too little humidity can be a danger to equipment in a data center. If the room is too humid, there is a risk of condensation building up on the equipment, which can cause corrosion and electrical shorts. If humidity is too low, the equipment can build up an electrostatic charge, resulting in dangerous static electricity. Either way, failing to monitor humidity can lead to significant unplanned downtime.
The cost of unplanned downtime varies depending on the size of a company. The average cost per minute of downtime at a data center is nearly $9,000. The American Society of Heating, Refrigerating and Air-Conditioning Engineers (ASHRAE) provided updated guidelines for relative humidity in data centers in 2016, after partnering with the University of Missouri to learn more about the impact of humidity on electrostatic discharge. These new guidelines suggest a minimum humidity of 20% and a maximum of 80%, with the ideal range falling between 45% and 55%. Monitoring humidity to ensure it’s within the recommended range will help keep your equipment functioning properly, saving maintenance and repair costs over time.

3. Airflow
Airflow monitoring is a central component of smart data center design. It’s responsible for pulling heat away from equipment and ensuring temperatures stay at appropriate levels. Using efficient airflow management techniques is essential for reducing energy costs. Airflow systems need attention through maintenance. Dust and dirt can block crucial airflow, which can quickly lead to damaged hardware.
Environmental monitoring should include quality airflow systems to ensure any issues are caught as soon as they arise and before they can harm data center equipment.
4. Power
Data centers consume an immense amount of power, and issues can arise if the flow of that power is shut off or interrupted. Even with the use of an uninterruptible power supply (UPS), electrical failures can force air conditioning to shut off. Without temperature control, the whole room can overheat at a rapid pace. Monitoring incoming current and planning for potential equipment shutdown in case of a power failure is a key part of minimizing risks. While the downtime involved is undesirable, it is preferable to experiencing equipment damages or failures due to overheating.
Voltage sensors are another form of power monitoring. They allow you to identify when a brownout is occurring by detecting line voltage or lack thereof. This helps with measuring UPS and the quality of your service provider’s performance.
Power consumption should also be monitored. Knowing how much power a piece of equipment is using is a key part of maximizing efficiency, and is one of the most important types of environmental monitoring for businesses that want to save money on operating costs.
5. Smoke
When a smoke alarm goes off, it may trigger a power shutdown. Because smoke alarms usually aren’t part of a system that alerts the IT team, the data center may be ignored in the event of an emergency. While managers at the facility may be notified and take action regarding the smoke, it often takes some time before someone thinks to inspect the server equipment.
One of the most effective ways to monitor this particular environmental factor is to integrate the alarms with your climate monitoring system. This way, your IT team can minimize downtime and damage if a smoke alarm causes the power to shut off.
In addition to power concerns, you also want to ensure your data center is free from fire suppression systems that use water. Water can severely damage technology equipment and systems like sprinklers could cause more harm than good if a nonemergency accidentally sets them off. To ensure your data center’s environment is truly conducive to efficiency, install waterless fire suppression measures that won’t damage your equipment in the case of a nearby fire or accidental alarm triggering.
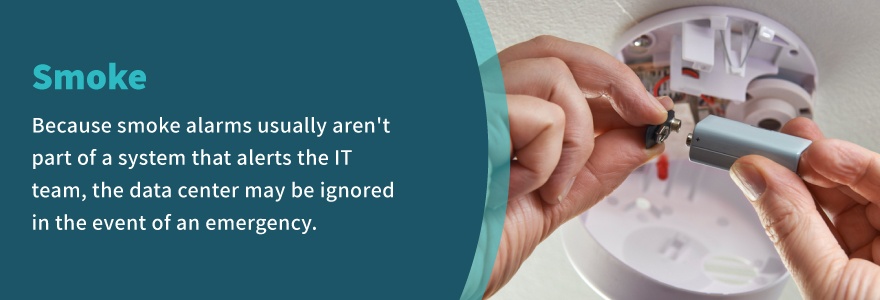
Benefits of Environmental Monitoring
Implementing environmental monitoring methodology in a new or existing data center is an investment that makes some IT managers pause. In some cases, the decision-maker will attempt to save money upfront by declining environmental monitoring, but quickly finds out their cost-cutting measure actually costs more. Here are three additional reasons to monitor your environment:
1. Increased Reliability
With environmental monitoring, equipment lasts longer. Between network and storage devices, cooling equipment and power distribution, there are many moving parts a data center manager has to know are working. One study asked managers how long it would normally take them to find a server that went down. Only 26% of them felt confident they could find the server within a few minutes. The majority, 58%, said they could locate the server in under four hours. About 20% said they would need more than a day.
With quality monitors, managers can locate faulty equipment faster. And with unprecedented control of factors like humidity and temperature, equipment will have a longer functional life.
2. Streamlined Workflow
Data center managers benefit from monitoring software that helps them control processes and workflow easier. When they have access to minute information like cooling efficiency, real-time data helps give a bird’s-eye view of the center’s infrastructure. If resources need to be re-allocated to address hot spots in the racks, a manager can do that in less time. Monitoring tools allow managers to take full advantage of IT infrastructure while decreasing energy costs.
3. Reduced IT Costs
A data center with robust environmental monitoring is less susceptible to inefficiencies that waste money. Management is more effective, allowing for less IT staff. Unused servers can be found and used or turned off to ensure they aren’t eating up energy. Monitoring also provides timely data managers can use to reduce the impact of failures or outages in equipment. The significant reduction in unplanned downtime makes the value of environmental monitoring evident.
4. Remote Sensing
Many types of environmental monitoring capabilities allow you and your leadership team to track changes in your data center, even when you’re away from the room or building. Cloud-based system controls help you manage some crucial environmental and threat detection applications from anywhere you can access the internet. Remote options also make monitoring your data center’s environment more convenient if your equipment is in a remote location.
5. Wider Visibility
Environmental monitoring’s remote features also allow you to monitor your entire data center all at once. You can rest assured knowing all components of your infrastructure are taken care of, so wherever issues arise, you’ll know about it right away. You can even choose to create a schedule for inspecting critical systems, so you can ensure all tech is operating in ideal conditions regularly.
6. Energy Efficiency
By monitoring your data center’s environment more intentionally, you can help your business reduce its energy use, saving you money.
For instance, upgrading your air conditioning system with new parts or improved airflow strategies can let technology operate at ideal temperatures without overtaxing temperature monitoring systems. Environmental monitoring often begins with analyzing your current data center setup and considering better ways to organize your technology so it’s in more ideal places in relation to cooling systems and power sources.
The Benefits of Network Monitoring and Threat Detection
For the most rigorous data defenses, combine environmental monitoring with network monitoring and threat detection. Given the huge and growing volume of data today’s organizations produce, no one person has the capacity to analyze all possible threats. Threat detection software monitors data analytics to uncover potential weak spots in your network, analyzes the level of the threat and helps determine what action must be taken to mitigate the threat.
In general, threat detection systems are comprised of software installed on every endpoint device. These devices connect to the main management platform, allowing staff to monitor the devices and access reporting. The central benefit of threat monitoring and detection is its hands-off nature. There is no need to assign a staff member to scan for possible threats, as the software does it for you in real-time, all the time.
Threat detection solutions have sophisticated insight into monitored data activity across the full range of endpoints, allowing the software to flag threats that a firewall or antivirus would miss. The types of anomalies that might cause the software to flag a threat include uncommon or suspicious processes, unrecognized connections and activities that might be considered risky. When the monitoring system detects a threat, the IT team can:
- Confirm validity of threats
- Waive false positives
- View and analyze relevant data
- Remove malicious files
- Halt suspicious processes
Types of Threat Detection
There is a range of network monitoring and threat detection options to choose from, each with pros and cons. It helps to group the types of threat detection into four categories.
1. Configuration Detection
Configuration-based detection compares the known architecture or design with activities on the network. Essentially, this form of detection looks for changes to the established baseline and alerts the appropriate party if the new activity is considered a threat.
This type of detection is easy for inexperienced analysts to work with, as it is the simplest. Because all malicious actions necessitate some deviation from the established baseline, configuration detection can theoretically catch all malicious activity. However, given the likelihood of routine changes in configuration, this method is best for more static environments.
2. Modeling Detection
Modeling detection works on a similar principle to the configuration type. However, instead of being told what constitutes normality, this approach mathematically builds a definition of normal and measures deviations from it over time. Modeling detection has fewer false positives than configuration and can detect malicious actions based on new changes.
The main disadvantage of modeling is that it takes a long period of training to establish a baseline. It will also require re-training to respond to changes in configurations and systems.
3. Indicators
Indicators are pieces of information that reveal a specific state as well as a context. In data security, there are good indicators, which identify legitimate files and activities, and bad indicators that can be used to flag threats. Indicators provide a quick way of pinpointing specific activities, allowing analysts to prioritize and respond to the activity faster than with other detection types.
The drawback of indicators is that they are retroactive rather than preventative. The activity must be observed and categorized before the indicator can be created, making indicators most useful as a companion to other types of detection.
4. Threat Behaviors
Threat behavior analytics is the most scalable method of threat detection. Threat behaviors define and codify the methods a malicious actor uses and provide a context for the activity. For example, if a remotely operated programmable logic controller (PLC) is accessed by a malicious actor through a virtual private network (VPN), the threat behavior would prompt an alert defined as a “supervisory control and data acquisition (SCADA) hijack”.
Detection based on threat behaviors is helpful because it has context baked in. Analysts don’t have to waste time determining why an alert has occurred, and instead can simply take action. This type of detection is also excellent at flagging unknown exploits.
Choosing a Threat Detection Service
Threat monitoring and detection services generally combine two or more types of detection for the most comprehensive coverage. The most advanced data management systems leverage machine learning to become more effective over time. The right monitoring and detection for your business depend on the size and industry of the organization.

According to the annual study by IBM and the Ponemon Institute, the cost of a data breach has increased to $3.92 million. More advanced solutions require a larger investment, but protecting your organization from data breaches will ultimately save money.
Taking Advantage of Network Monitoring
The most effective utilization of network monitoring and threat detection involves a few different steps beyond choosing software. These best practices will help ensure your monitoring solution is being employed to its full potential:
- Monitor every endpoint that can be used to access the network.
- Set rule-based alerts for suspicious or risky activity.
- Build monitoring solutions and data detection with preventative tools like antivirus and firewalls.
- Provide a solid foundation of monitoring with data protection like encryption and classification.
The human element of network monitoring is critical, as well. Recent data suggests more than 80% of all data breaches are the inadvertent result of human error, so providing comprehensive and ongoing cybersecurity training for all employees is a step you shouldn’t skip.
Developing an incident response plan is also imperative. Preventative measures are always preferable to reactivity, but threat monitoring and detection will be less powerful tools if there is no plan in place to respond to security events when they do occur.
Video Surveillance
In addition to environmental and threat monitoring, every business can benefit from high-quality video surveillance. These three characteristics are the most important for a video surveillance system:

1. High-Quality Imaging
The point of video surveillance is to monitor what’s going on, but it doesn’t help when the video quality is sub-par. A fuzzy analog video might show you that an unauthorized individual has gained access to your facility, but it won’t help you spot any identifying features.
Today’s video surveillance systems can capture high-definition images that are significantly more actionable. For instance, if theft or damage to a piece of equipment occurs, a good video surveillance system may help with the identification of the perpetrator.
High-quality video may also help improve productivity. When employees know they are being monitored and can likely be identified by video, they will be less likely to stand around when they should be performing their duties.
2. Systems Integration
Video surveillance is most valuable when it works with your environmental monitoring tools. For instance, if a smoke alarm goes off, your surveillance system allows you to quickly view the server room to ascertain whether the equipment is actually in the path of a fire.
Surveillance can also be used to enhance the information delivered by environmental alerts. If you receive an alert that your cooling system is not functioning at full capacity, you can coordinate timestamps from the video with scheduled maintenance to check whether the correct scheduled maintenance was performed on the affected area of the system.
A system that enables remote viewing makes it easier for IT managers to get the most out of environmental monitoring from anywhere in the facility.
3. Flexible Storage
The storage of surveillance footage has evolved rapidly over the past few decades. Frame rates and increasingly high resolutions have changed the landscape of storage almost entirely. By 2020, more than 3 trillion hours of surveillance video will be captured annually. This increase in quality and quantity of footage means a network video recorder that could once have supported 100 cameras may only be able to support around 20 today.
Flexible or “intelligent” storage is the foundation for the smart use of video surveillance systems. Storing footage for at least one year is recommended, but it is impractical to do that on hard disks. Storage costs differ based on the medium, so having multiple tiers to choose from can result in significant savings.
Footage that’s considered high-priority or files that are frequently used are best kept on a performance-oriented disk. Files with lower priority don’t need to be accessed as frequently and can be saved to a cloud or kept on tape.
Even though the architecture is tiered, the best video management systems (VMS) offer a single file system view in which footage can be viewed and managed with ease.

Improve Your Data Center With DataSpan
A data center houses your company’s most critical asset: information. To protect that information and your equipment investment, you need robust environmental monitoring. From physical factors to network monitoring and video surveillance, DataSpan has the expertise to bring better security to your business.
DataSpan has 50 years of experience in IT physical infrastructure, data center IT services and data storage. We’ve served thousands of businesses with unique needs and challenges, and tailored specialized solutions that optimize the storage and security of data. No matter what technological challenges your company faces, DataSpan is committed to overcoming them.
Our data center products and services cover every area of operation, from basic equipment to sophisticated service solutions. The products we offer include:
- Structured cabling
- Data center infrastructure management (DCIM)
- Technical furniture
- Raised floor systems
- Racks and enclosures
- Power solutions
- Cooling solutions
- Hot and cold aisle solutions
- Airflow products
We provide more than environmental monitoring as well. Our range of services covers everything from cleaning and consulting to data center moves and relocations. If you’re interested in any of our expert services and trusted products, get in touch with us by calling (800) 660-3586 or filling out our contact form. We’re happy to answer your questions on environmental monitoring and other data center and networking services.